Cisco ASA to Palo Alto Migration Tool
Stop spending weeks manually converting ASA configs to PAN-OS. NetConverter's comprehensive multi-step pipeline automates the translation of security policies, NAT rules, and object groups with 95%+ accuracy and confidence scoring.
Why Cisco ASA → Palo Alto Migrations Are Hard
If you're moving from Cisco ASA 9.x or 9.18 to Palo Alto PAN-OS 11.2 (Strata or Panorama-managed), the toughest semantic gap isn't the syntax — it's that ASA's interface-based security levels don't have a 1:1 equivalent in Palo Alto's zone-based policy model. A typical 8,000-rule ASA config translates to roughly 4,500–6,000 PAN-OS security rules after de-duplication, with NetConverter's pipeline averaging 96.4% accuracy on production-scale conversions.
The non-obvious migration killers we see most often: (1) ASA object network with embedded NAT rules (auto-NAT) that need to split into separate Palo Alto NAT policies; (2) ASA service object-groups containing mixed TCP/UDP services that PAN-OS requires you to split into single-protocol service objects; (3) ASA access-group applied globally vs per-interface, which changes zone-pair derivation; and (4) ASA nameif values like outside/inside/dmz that engineers expect to map automatically — but only do so when zone-inference patterns are pre-loaded into the KB. NetConverter handles all four deterministically.
The Challenge of ASA to Palo Alto Migration
Different Security Models
ASA uses interface-based security levels while Palo Alto uses zones. Manual mapping takes hours and is error-prone.
NAT Complexity
ASA's object NAT and twice NAT don't map directly to PAN-OS NAT policies. Each rule requires careful translation.
Object Group Translation
Network objects, service objects, and object-groups must be converted to address objects and service objects.
ACL to Security Policy
Extended ACLs with complex matching criteria need to be converted to zone-based security policies.
How NetConverter Solves It
Vendor-Neutral Translation
Our comprehensive multi-step pipeline normalizes configurations to a unified format, enabling accurate translation between any vendor pair.
Automatic Zone Mapping
AI-assisted zone mapping analyzes your ASA topology and recommends optimal Palo Alto zone assignments.
Intelligent NAT Conversion
Both object NAT and twice NAT are correctly translated to PAN-OS NAT policies with proper rule ordering.
Complete Object Migration
All network objects, service objects, and groups are automatically converted with naming conventions preserved.
4-Tier Validation System
Every translation undergoes comprehensive validation: syntax correctness, semantic accuracy, vendor best practices compliance, and AI-assisted review.
Confidence Scoring
Each conversion includes a confidence score indicating translation quality, helping you prioritize review efforts and ensuring production readiness.
Panorama & App-ID Ready
Generate Panorama-ready device groups and templates. Our engine suggests App-IDs based on service rules and traffic patterns.
Pre-Migration Cleanup
Identify and remove unused objects, shadowing rules, and duplicates on your ASA config *before* migration ensures a clean target policy.
Advanced Context Mapping
Seamlessly translate Cisco Multi-Context configurations to Palo Alto VSYS or Device Groups, maintaining logical separation.
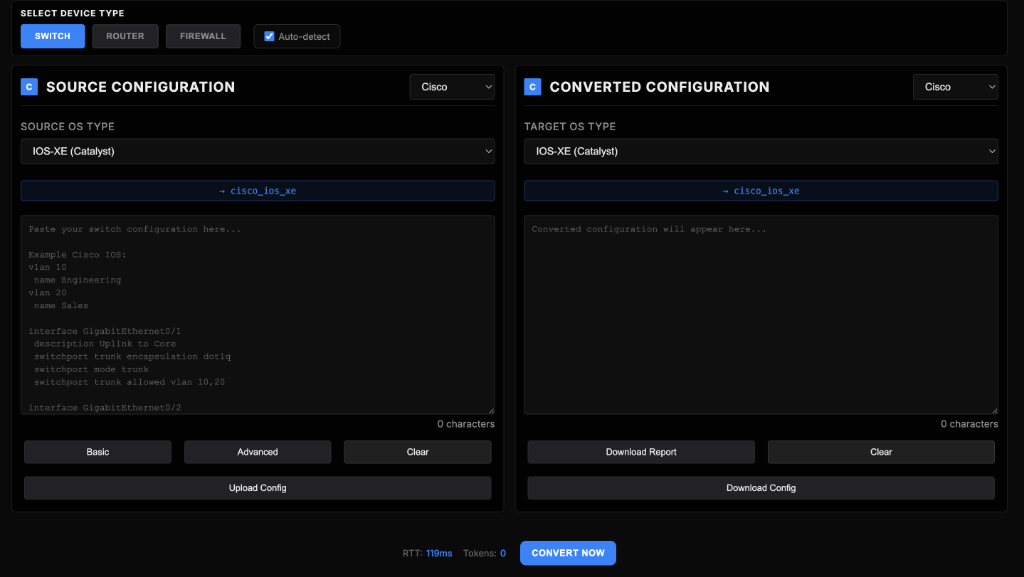
See Quick Convert Output in Action
Representative Quick Convert run for this migration path, showing the live NetConverter interface and the converted output preview engineers review before deployment.
Migration Results
Why Teams Choose This Over Vendor Tools
Vendor tools are destination-locked
Expedition focuses on Palo Alto onboarding workflows and does not provide independent cross-platform validation for mixed-vendor programs.
NetConverter adds validation gates
Each conversion includes reference and structure checks so teams can catch missing objects and policy drift before production push.
Built for enterprise migration waves
Use repeatable conversion for ASA estates, with deterministic output plus support for complex NAT, object-group, and policy constructs.
Need Custom Development or Complex Migration Support?
For large-scale enterprise migrations, custom protocol requirements, or dedicated engineering support, our team is here to help.
Ready to Migrate?
Convert your Cisco ASA configuration to Palo Alto PAN-OS in minutes. No credit card required.
Start Free MigrationFrequently Asked Questions
How does Cisco ASA object-NAT translate to Palo Alto?
object network WEB with embedded NAT becomes one PAN-OS address object plus one NAT rule, with the original_destination + translated_destination resolved via name lookup. Twice-NAT (manual NAT) translates more cleanly because it's already a separate construct in both vendors.Will my ASA security-level zones (inside/outside/dmz) map to Palo Alto zones automatically?
inside, outside, dmz, management, and security-level numbers, and map them to Palo Alto zones (Trust/Untrust/DMZ/Mgmt) using KB-defined rules. Custom nameifs trigger a flag asking you to confirm the zone mapping before output. The result is reviewable in Conversion Studio's zone matrix view.